When it comes to holding cryptocurrency, the biggest risk isn’t hacking or market crashes-it’s losing access to your own money because you trusted too much to one person, one device, or one key. A MultiSig wallet fixes that. It doesn’t just add security-it changes how you think about control. Instead of one private key holding all the power, a MultiSig wallet requires two or more signatures before any transaction can go through. Think of it like a bank vault that needs two keys to open: one held by you, another by your trusted partner. If one key is lost, stolen, or compromised, your funds stay safe.
How MultiSig Wallets Actually Work
A MultiSig wallet uses an M-of-N system. That means out of N total keys, you need M signatures to move funds. The most common setup is 2-of-3: you have three separate keys, and any two of them can approve a transaction. This isn’t just theory-it’s what companies like Gnosis Safe and Casa use every day. The wallet itself is a smart contract on the blockchain, not a simple app. It doesn’t store coins; it enforces rules. Only when the required number of people sign does the contract release funds.
Why does this matter? Because single-key wallets are fragile. Remember Quadriga? In 2019, the exchange lost over $115 million when its founder died-and he was the only person with access to the private keys. No backups. No alternatives. Just silence. A 2-of-3 MultiSig would have let the other two signers move the funds. No loss. No drama.
Choosing the Right M-of-N Setup
Not all MultiSig wallets are built the same. Your setup should match your risk level and how you use the money.
- 2-of-3: Best for individuals or small teams. One key on your hardware wallet, one on a backup device, one with a trusted friend or family member. If you lose one, you still have two ways to recover.
- 3-of-5: Used by businesses, DAOs, or large holders. Distributes control across multiple people-CEO, CFO, CTO, legal rep, and an external auditor. No single person can act alone.
- 1-of-1: Not MultiSig. Avoid this. It’s just a regular wallet with extra steps.
Don’t go too high. A 5-of-7 might sound secure, but if one person disappears, you’re stuck waiting for five others to coordinate. Complexity kills usability. Simplicity kills security. Find the middle.
Hardware Wallets Are Non-Negotiable
Signing keys on your phone or laptop? That’s like locking your money in a cardboard box and leaving it on the street. Every signer in your MultiSig setup should use a dedicated hardware wallet-like a Ledger Nano X or a Trezor Model T. But here’s the catch: don’t use the same brand for all keys.
Why? Because if all your keys are on Ledger devices, and Ledger has a firmware vulnerability, all your keys are at risk. Use different manufacturers: one Ledger, one Trezor, one Keystone. This is called hardware diversity. It stops a single flaw from wiping out your entire setup.
Also, never reuse a hardware wallet that’s been used for a hot wallet. If a key was ever connected to an exchange or a DeFi app, it’s compromised. Generate new keys, fresh from the factory.

Geographic Separation and Air-Gapped Signing
Don’t keep all your hardware wallets in the same house. If there’s a fire, flood, or burglary, you lose everything. Store one key in your home, another in a safety deposit box in another city, and the third with a trusted person in a different country. This isn’t paranoia-it’s standard practice for institutional investors.
When signing a transaction, do it on a device that’s never been connected to the internet. Use a clean laptop, boot from a live USB, and disconnect Wi-Fi. This is called air-gapping. Even if malware infects your phone, it can’t touch a key that’s never been online.
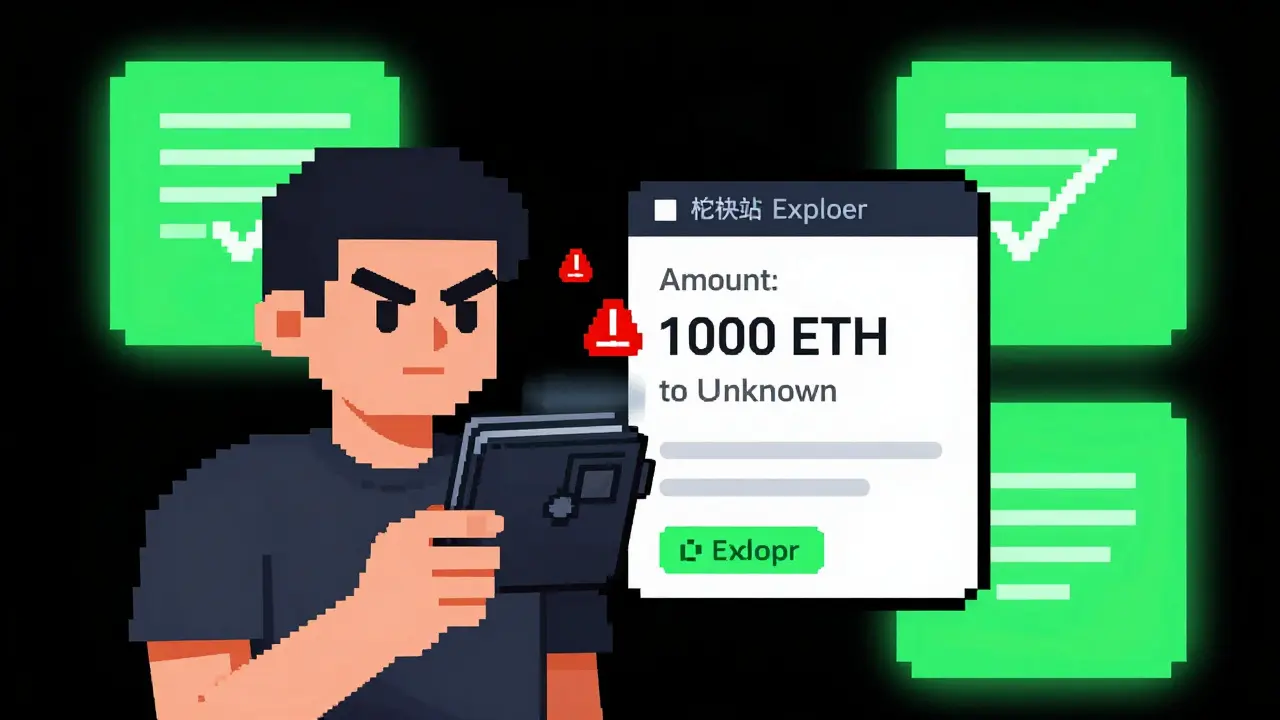
Transaction Verification Is Your Last Line of Defense
Signing a transaction without checking it is like handing over your house keys to someone who says, “I’m going to fix the roof.” You don’t ask questions-you just sign. But with MultiSig, you must ask.
Before you sign, verify:
- The exact address you’re sending to
- The amount
- The token type (is it ETH? USDC? Or a scam token?)
- Any smart contract function being called (like a swap or approval)
Use tools like Etherscan or Blockchain explorers to double-check. If the transaction says “approve 1000 ETH to 0x7a…c3b9,” and you didn’t set up a swap, don’t sign. That’s a phishing attack. Even if you have 2-of-3, one bad signature can drain everything.
Backup Everything-And Store It Separately
MultiSig isn’t just about keys. You also need the wallet’s Output Descriptor. This is a file that tells the wallet how to reconstruct the address. If you lose it, you can’t recover funds-even if you have all the keys.
Write down your recovery phrases on metal plates. Store them in waterproof, fireproof containers. Keep one at home, one in a bank vault, one with your lawyer. Never store them digitally. No cloud. No encrypted drive. No screenshot. Paper or metal only.
Also, write down the exact M-of-N configuration. If you forget you’re using 3-of-5, you’ll waste weeks trying to get five people to sign.
Monitor, Review, and Update
MultiSig isn’t a set-it-and-forget-it system. You need to monitor it.
- Use tools like Safe Watcher to get alerts for every proposed transaction.
- Review who has signing power every six months. Did someone leave the company? Did a key holder get hacked?
- Have a plan for replacing a lost or compromised key. You should be able to remove a signer and add a new one without moving funds.
- Enable 2FA on any account linked to your wallet-email, wallet provider, or exchange.
And never skip the review. One company lost $2 million because they didn’t check who had access. A former employee still held a key. He used it to drain funds. They didn’t know he still had access.
What MultiSig Won’t Fix
MultiSig isn’t magic. It won’t protect you from:
- Phishing emails that trick you into signing fake transactions
- Malware that steals your recovery phrase
- Someone with physical access to your hardware wallet if they know your PIN
- Bad decisions-like using the same key for your savings and your DeFi trades
It’s a tool, not a shield. You still need discipline.
Final Rule: Trust, But Verify
The best MultiSig setup in the world fails if you stop asking questions. Always verify. Always double-check. Always test recovery. Do a mock transaction with small amounts. Make sure your backup works. Ask your co-signers if they can sign. Call them. Text them. Confirm.
MultiSig doesn’t just protect your money. It protects your peace of mind. You won’t wake up in a cold sweat wondering if your entire life savings vanished because one person died, got fired, or got hacked. You’ll know-because you planned for it.
What’s the best MultiSig configuration for a regular user?
For most people, 2-of-3 is ideal. Keep one key on your hardware wallet, one on a backup device stored securely at home, and one with a trusted family member or friend who lives in a different location. This balances security, accessibility, and simplicity. Avoid going higher than 3-of-5 unless you’re managing institutional funds.
Can I use the same hardware wallet for multiple signers?
No. Using the same device for multiple keys defeats the purpose. If that device is stolen, damaged, or compromised, all your keys are at risk. Always use different hardware wallets from different manufacturers-for example, one Ledger, one Trezor, and one Keystone. This is called hardware diversity and is critical to avoid single points of failure.
Do I need to back up the Output Descriptor file?
Yes. The Output Descriptor tells your wallet how to reconstruct the address from your keys. Without it, even having all your private keys won’t let you recover your funds. Write it down on paper and store it with your recovery phrases-preferably in a separate, secure location.
What happens if one of my co-signers dies or disappears?
If you’re using 2-of-3 or 3-of-5, you can still access your funds with the remaining signers. That’s the whole point. But you should have a pre-planned process to replace the lost signer-like adding a new key or updating the wallet’s configuration. Always document this procedure and share it with all signers.
Is MultiSig safer than a single-key wallet?
Absolutely. A single-key wallet has one point of failure: if that key is lost, stolen, or compromised, your funds are gone. MultiSig spreads risk across multiple keys and people. Even if one key is stolen, the attacker still needs two or more others to move funds. The Quadriga collapse proved how deadly single-key systems can be. MultiSig prevents that.







Marie Mapilar
March 25, 2026 AT 04:16PS: I typo’d 'Trezor' as 'Trezor' in my notes once. Almost signed a tx with the wrong key. Learned my lesson.
Dominic Taylor
March 26, 2026 AT 16:50Shelley Dunbrook
March 27, 2026 AT 10:39Aman Kulshreshtha
March 28, 2026 AT 21:27Leona Fowler
March 29, 2026 AT 11:44Neil MacLeod
March 31, 2026 AT 09:30Misty Williams
April 1, 2026 AT 19:22Anand Makawana
April 2, 2026 AT 19:09Mohammed Tahseen Shaikh
April 4, 2026 AT 17:14Sarah Terry
April 4, 2026 AT 17:16Shayne Cokerdem
April 5, 2026 AT 20:18aravindsai pandla
April 6, 2026 AT 04:39namrata singh
April 6, 2026 AT 23:07Zion Banks
April 8, 2026 AT 08:09Annette Gilbert
April 9, 2026 AT 06:35John Alde
April 10, 2026 AT 18:09manoj kumar
April 11, 2026 AT 00:02