Imagine handing over the keys to your entire digital life-a family photo archive, sensitive business contracts, or personal health records-to a single company. That is exactly what happens when you use traditional cloud storage. Now imagine that same data being shattered into millions of encrypted puzzle pieces, scattered across thousands of computers worldwide, where no single entity-not even the service provider-can reconstruct it without your permission. This is the promise of decentralized storage security.
In 2026, the conversation around data safety has shifted dramatically. We are no longer just asking if our data is backed up; we are demanding control over who sees it and how it survives potential breaches. Centralized systems have served us well for decades, but their inherent weakness-a single point of failure-makes them attractive targets for hackers and vulnerable to corporate censorship. Decentralized storage flips this model on its head, offering a robust alternative rooted in cryptography and distributed networks.
The Core Mechanism: Encryption and Fragmentation
To understand why decentralized storage is secure, you first need to grasp how it handles your files. Unlike a traditional server that stores your document as one complete file, decentralized systems break your data down. This process is called data fragmentation.
Here is how it works in practice:
- Encryption: Before your data leaves your device, it is encrypted using strong cryptographic protocols. This means the information is scrambled into unreadable code. Only you hold the key to unscramble it.
- Sharding: The encrypted data is split into small fragments or shards. These pieces look like random noise to anyone intercepting them.
- Distribution: These shards are sent to different nodes (computers) across a global peer-to-peer network. No single node holds enough information to reconstruct your original file.
This architecture creates a formidable barrier against unauthorized access. Even if a hacker compromises several nodes in the network, they only obtain useless fragments of encrypted data. Without the encryption key and the correct combination of shards, the data remains inaccessible. This client-side encryption ensures that privacy is maintained from the moment you upload a file.
Eliminating Single Points of Failure
The most significant vulnerability in traditional centralized storage is the single point of failure. If Amazon’s servers go down, or if a data center in Northern Virginia suffers a power outage, millions of users lose access to their data simultaneously. In 2025, we saw several high-profile outages that disrupted businesses globally, highlighting this fragility.
Decentralized storage eliminates this risk by design. Because data is replicated across multiple independent nodes, the failure of one or even dozens of nodes does not impact data availability. The network automatically reroutes requests to healthy nodes holding copies of the required shards. This redundancy ensures continuous uptime and resilience against physical disasters, hardware failures, and targeted attacks.
Consider a natural disaster scenario. A hurricane might destroy a major data center hosting centralized backups. In a decentralized network, the data shards are stored in locations ranging from rural farms in Germany to residential PCs in Japan. The loss of one geographic region does not compromise the integrity of the dataset. This geographical distribution is a core tenet of distributed ledger technology applied to storage.
Resistance to DDoS Attacks and Censorship
Distributed Denial-of-Service (DDoS) attacks remain a primary threat to online services. Attackers flood a central server with traffic, overwhelming its capacity and causing it to crash. Since decentralized networks lack a central server, there is no single target to overwhelm. An attacker would need to simultaneously flood thousands of geographically dispersed nodes, which is economically and technically impractical.
Beyond technical attacks, decentralized storage offers resistance to censorship. In centralized models, providers can remove content based on government pressure or internal policies. With decentralized systems, once data is uploaded and its hash recorded on a blockchain, it becomes nearly impossible to delete or alter without detection. This immutability makes these platforms ideal for preserving historical records, journalistic archives, and other sensitive information that requires long-term integrity.
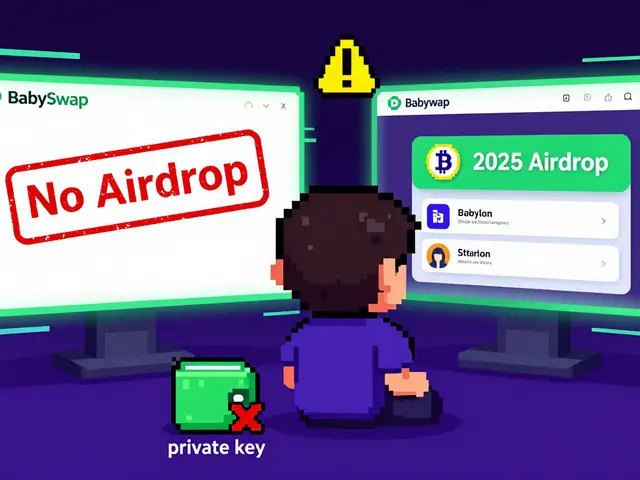
Key Management: The User’s Responsibility
While decentralized storage enhances security, it shifts responsibility to the user. In traditional cloud services, if you forget your password, a support team can reset it. In decentralized systems, your encryption keys are yours alone. There is no "forgot password" button because no one else knows your key.
This presents a double-edged sword:
- Pros: Complete privacy. Not even the platform operators can access your data.
- Cons: If you lose your keys, your data is permanently lost. There is no recovery path.
Users must adopt rigorous key management practices. This includes storing private keys in secure hardware wallets, using mnemonic phrases stored in safe locations, and understanding the importance of regular backups. As the industry matures, user interfaces are becoming more intuitive, but the underlying principle remains: sovereignty comes with accountability.
| Feature | Centralized Cloud (e.g., AWS, Google Drive) | Decentralized Storage (e.g., IPFS, Filecoin) |
|---|---|---|
| Data Control | Provider-controlled | User-controlled via encryption keys |
| Failure Risk | Single point of failure | Distributed redundancy |
| Censorship Resistance | Low (provider can delete content) | High (immutable hashes) |
| DDoS Vulnerability | High | Very Low |
| Privacy Level | Moderate (provider may scan data) | High (end-to-end encryption) |
| Key Recovery | Supported by provider | User responsibility only |
Leading Platforms and Architectures
Not all decentralized storage solutions are created equal. Two prominent names dominate the landscape: IPFS (InterPlanetary File System) and Filecoin.
IPFS is a protocol that allows users to share files in a distributed manner. It uses content addressing rather than location addressing. When you request a file, you ask for its specific hash, not its server location. This ensures you always get the exact version of the file you intended, preventing tampering. However, IPFS itself does not guarantee long-term storage; nodes may stop hosting files at any time.
Filecoin builds on IPFS by adding an economic layer. Users pay miners to store their data for a specified period. Miners compete to offer storage space at lower prices while proving they still hold the data through cryptographic proofs. This incentivizes reliability and longevity, making Filecoin suitable for enterprise-grade archival needs.
Other emerging platforms like Arweave focus on permanent storage, charging a one-time fee for data to be stored forever. Each platform has distinct security features and trade-offs regarding cost, speed, and permanence. Choosing the right solution depends on your specific use case-whether you need temporary caching, long-term backup, or immutable record-keeping.
Implementation Challenges and Best Practices
Adopting decentralized storage requires a shift in mindset and operational procedures. Organizations moving from traditional clouds must address several challenges:
- Latency: Retrieving data from a distributed network can be slower than accessing a local server. Optimizing retrieval speeds often involves pinning data to nearby nodes.
- Cost Structure: While long-term costs may be lower due to reduced reliance on expensive enterprise servers, initial integration and gas fees (on blockchain networks) can add complexity.
- Talent Gap: Managing decentralized infrastructure requires specialized knowledge in cryptography and network dynamics. Training teams is essential.
Best practices include conducting thorough audits of chosen platforms, implementing multi-layered encryption strategies, and maintaining hybrid setups during transition periods. Start with non-critical data to test performance and reliability before migrating sensitive assets.
The Future of Data Sovereignty
As regulations like GDPR and CCPA tighten, the demand for user-centric data solutions grows. Decentralized storage aligns perfectly with these legal frameworks by giving individuals direct control over their information. By 2027, we expect mainstream adoption among enterprises seeking to mitigate supply chain risks and enhance privacy compliance.
The trajectory is clear: as centralized vulnerabilities become more apparent, decentralized architectures will transition from niche alternatives to standard security practices. The key lies in balancing innovation with usability, ensuring that robust security does not come at the expense of accessibility.
Is decentralized storage safer than cloud storage?
Yes, in terms of resilience and privacy. Decentralized storage eliminates single points of failure and uses end-to-end encryption, making it harder for hackers to breach and for providers to censor. However, it requires users to manage their own encryption keys, which adds complexity compared to traditional cloud services.
What happens if I lose my encryption key in decentralized storage?
If you lose your encryption key, your data is permanently inaccessible. Unlike centralized services, there is no customer support to recover your account. You must store your keys securely, such as in a hardware wallet or a safe deposit box, and create redundant backups.
How does IPFS differ from Filecoin?
IPFS is a protocol for sharing files in a distributed way, but it does not guarantee long-term storage. Filecoin is a marketplace built on top of IPFS where users pay miners to store data for a set period, ensuring reliability and longevity through economic incentives.
Can decentralized storage prevent DDoS attacks?
Yes. Because decentralized networks distribute data across many nodes, there is no central server to overwhelm with traffic. Attacking the entire network simultaneously is practically impossible, making it highly resistant to DDoS attacks.
Is decentralized storage suitable for beginners?
It is becoming easier, but it still requires more technical understanding than traditional cloud storage. Beginners should start with user-friendly platforms that abstract some complexities, but they must still learn responsible key management to avoid data loss.